CASE STUDY:
REDESIGNING A TIER-ZERO RESOURCE ORCHESTRATION PLATFORM
Improving data governance and usability within a financial institution
Due to confidentiality agreements, some details of this project have been generalised and certain elements of the system have been simplified while preserving the core design challenges and outcomes.
I joined the project as a Frontend Developer before transitioning into a UX role on a tier-zero platform within a major financial institution during a critical modernisation phase.
The interface had not been meaningfully updated since 2015 and the system had accumulated significant structural and data debt. The platform coordinated suppliers, consumers, resources and security policies across development, testing and production in a highly regulated environment.
After assessing the architecture, it became clear that simply transferring the existing structure into a new database was not a suitable solution. I revisited assumptions about hierarchy, visibility and access control.
My role evolved from implementing interface improvements to ensuring that architectural decisions were grounded in real user behaviour, operational constraints and governance requirements before migration began.
Summary
Identified and quantified 15-20% artefact/test data prior to migration.
Influenced the redesign of migration tooling based on structural findings.
Prevented inconsistencies in supplier group hierarchy redesign.
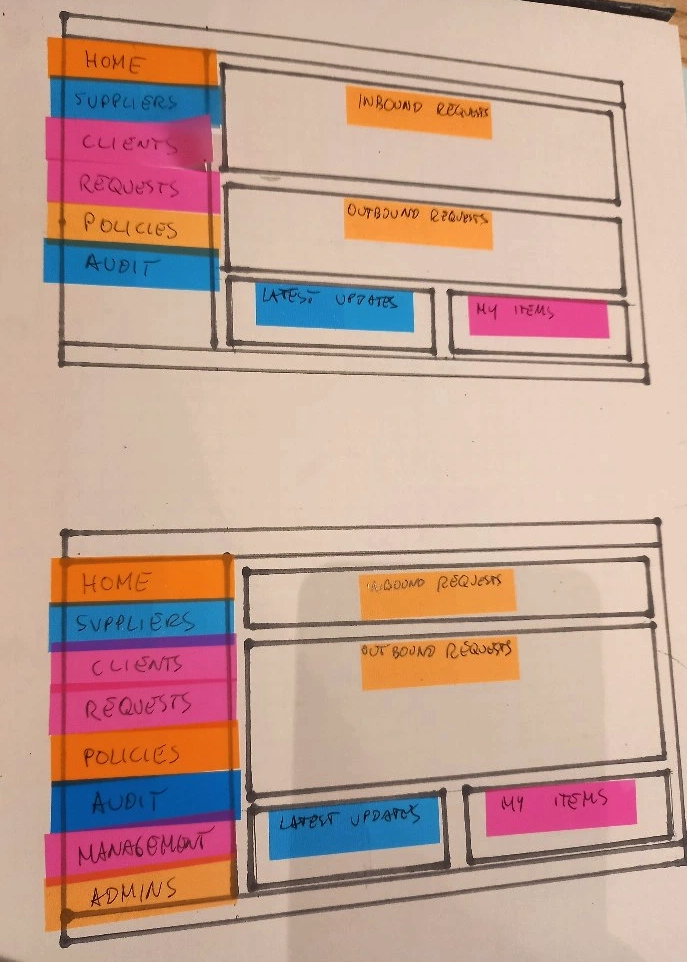
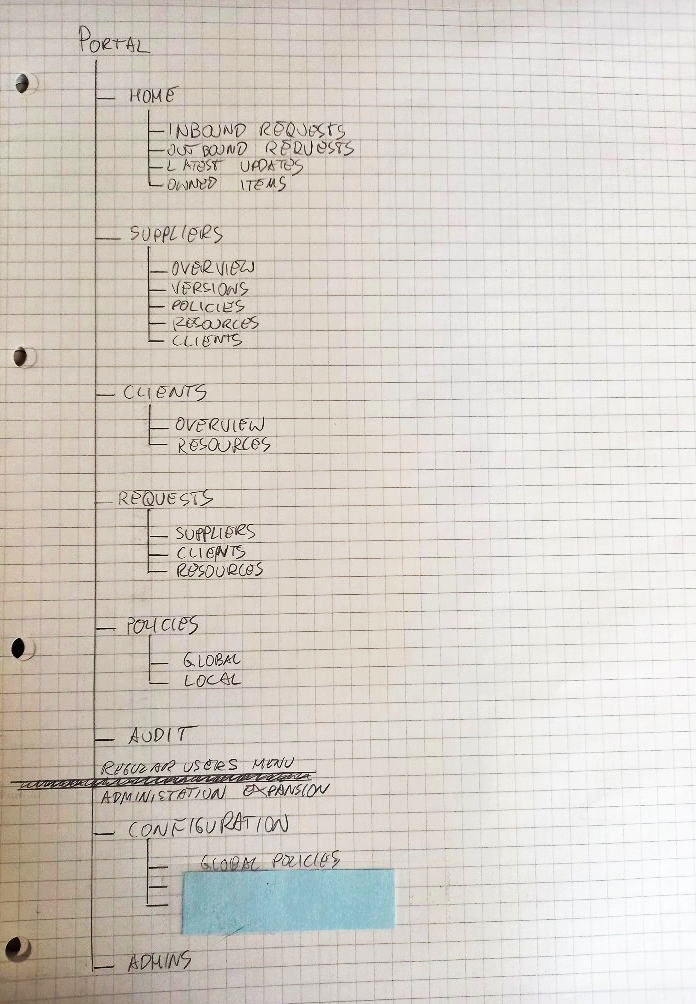
Introduced role-based data visibility aligned with governance principles.
Reduced unnecessary data exposure.
Minimised user workarounds through structural UX improvements.
Standardised the interface using the corporate design system.
Outcome
My involvement spanned two distinct phases over several years, reflecting a progression from implementation to structural influence.
Phase 1 – Modernisation & UX Transition
I joined the project as a junior Frontend Developer and spent nearly two years working closely with the UX Designer to implement a redesigned interface for a legacy system that had not been significantly updated since 2015.
In addition to implementation, I was responsible for validating user flows against documented research, pain points and usage scenarios. Through manual testing of prototypes and development builds, I developed a detailed understanding of how suppliers, consumers and administrators interacted with the platform across environments.
During this phase I gradually moved into UX responsibilities. I began creating and testing prototypes, contributing to interaction decisions and ensuring the new interface aligned with the corporate design system.
One of the major architectural improvements introduced during this stage was enabling clearer activation and management of resources across development, testing and production environments on the consumer side.
While validating workflows, I discovered that many users kept external notes containing supplier or resource identifiers so they could quickly resume work where they had left off. This behaviour later informed the introduction of a homepage dashboard showing each user’s most recent activity.
During this phase I also onboarded a new graphic designer to the project, helping transfer product knowledge and collaborate on translating wireframes into the final interface.
Phase 2 – Architectural Planning & Migration Preparation
During preparation for database migration and structural redesign, my role expanded beyond interface delivery into system-level thinking.
I worked closely with solution architects and backend engineers to ensure proposed architectural changes reflected real user workflows and enterprise governance requirements.
Conducting structured database audits to identify artefact, duplication and inactive entity patterns.
Analysing legacy user accounts that had not been cleared despite organisational changes.
Mapping current user journeys against proposed hierarchical models.
Designing role-based data visibility segmentation aligned with least-privilege principles.
Creating low-fidelity wireframes to model structural and grouping changes.
Identifying usability and security risks in proposals that exposed excessive data.
Supporting API logic discussions where workflow clarity was required.
Validating assumptions through user interviews before structural decisions were finalised.
During architectural discussions, some proposals suggested exposing large data tables across the interface so users could access all available information directly.
By presenting workflow analysis and structural findings to architects and stakeholders, I helped guide discussions towards solutions that better aligned with operational reality and governance requirements.
The patterns identified through this analysis influenced adjustments to the migration tooling and helped prevent structural inconsistencies within complex supplier group hierarchies that had evolved from long-standing user workarounds.
My Role
Migration planning exposed accumulated structural weaknesses:
15-20% of entities were artefacts created for informal testing.
Inactive or departed users remained present in the database.
Team-based access management had not been structurally implemented.
Users created temporary consumer entities to test resources.
Access models no longer reflected how teams operated in practice.
Large supplier groups contained layered or circular relationships introduced over time.
These issues reflected long-standing technical debt and governance drift within a security-critical internal platform.
The Problem
The project operated within strict enterprise limitations:
Tier-zero security classification.
Highly secured internal database with no external exposure.
In-house authentication and access management integration.
Mandatory use of corporate design system components.
Governance-driven architectural decision-making.
Limited flexibility for large-scale backend restructuring.
Migration executed under operational continuity requirements.
All design and structural decisions had to operate within these constraints.
Constraints
Key Challenges
Data Integrity Before Migration
Database analysis revealed that a significant proportion of entities were artefacts or redundant test entries. Allowing these structures to migrate unchanged would have embedded existing inconsistencies into the new system.
By quantifying and categorising these patterns, I helped ensure that migration tooling addressed structural issues rather than replicating them.
Supplier Group Hierarchy Redesign
A proposed restructuring aimed to consolidate large supplier groups into clearer parent-child hierarchies.
However, analysis revealed layered and circular connections introduced through historical testing and temporary configurations. Some consumer entities were both members of and independently connected to the same groups, creating structural conflicts under the new model.
I mapped these patterns, highlighted associated risks and contributed to adjustments in both migration preparation and interface modelling to prevent inconsistencies.
Data Visibility and Governance Alignment
Initial proposals included exposing large unified data tables to users. I evaluated these proposals against actual workflow requirements and identified unnecessary data exposure and cognitive overload risks.
The adopted approach implemented segmented, role-based visibility - extending access where operationally required while reducing unnecessary exposure for standard roles.
Reducing Workarounds
User interviews revealed reliance on external tracking of frequently used supplier and resource identifiers.
To reduce dependency on informal processes, I introduced structural improvements including:
Recent activity visibility.
Clearer team-based supplier access.
Structured onboarding flows.
Improved environment activation clarity.
These adjustments reduced friction without requiring radical interaction changes.
This project addressed structural debt within a security-critical enterprise platform while preparing for database migration.
By combining workflow validation, data analysis and architectural collaboration, I contributed to:
Cleaner migration preparation.
Reduced artefact propagation.
Improved hierarchy modelling.
Stronger governance alignment.
More secure and role-appropriate data visibility.
Reduced reliance on informal user workarounds.
It marked my progression from frontend delivery into UX-informed architectural influence within a tightly governed enterprise environment.